Executive Summary
The DrugHub Darknet Hub operates as a highly specialized, decentralization-focused hidden service utilizing the Tor anonymity network. It was established with the primary directive of facilitating the exchange of digital commodities and specialized physical goods under a strict privacy mandate. Unlike multifaceted platforms that rapidly expand into generalized commerce, this architecture maintains a narrow, optimized focus on cryptographic security and resilience against external disruption.
Independent observers note that the platform heavily prioritizes operational security (OpSec) over user convenience. By eliminating traditional friction points associated with localized wallet vulnerabilities, the network enforces modern standards for anonymous digital trade. This rigorous approach effectively isolates the hub from many attack vectors common to earlier iterations of darknet infrastructure.
Historical Timeline
Architectural Genesis
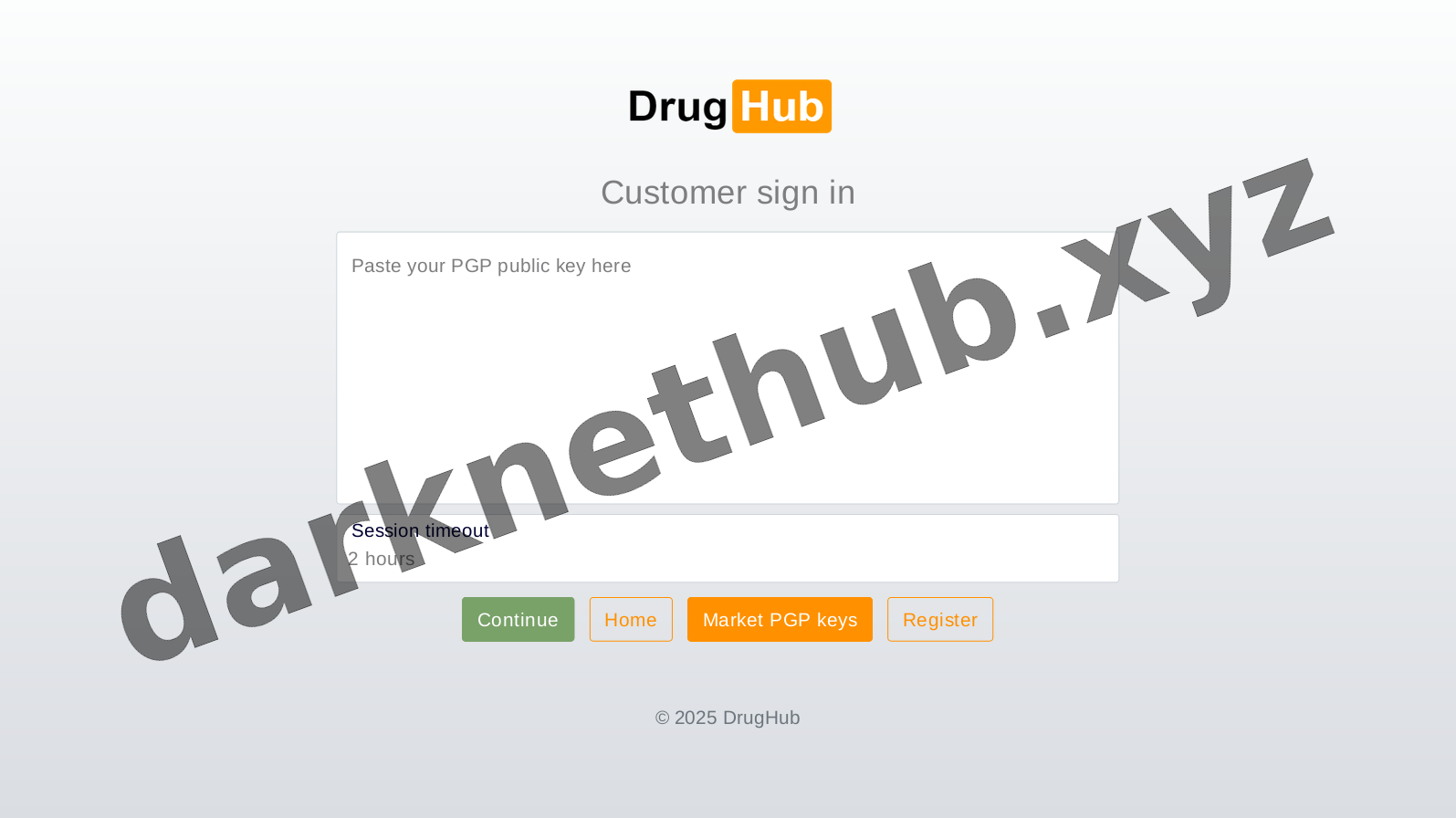
The core infrastructure was initially developed and deployed to the Tor network. Early iterations of the platform focused on stabilizing the load-balancing mechanisms and establishing the foundational PGP authentication routines required for secure access.
Mandatory PGP Integration
Observing critical weaknesses in traditional password-based authentication across parallel networks, administrators implemented a strict passwordless protocol. All client and merchant registrations began requiring complete cryptographic handshakes via public key infrastructure.
Monero (XMR) Exclusivity
To mitigate blockchain analysis and ledger tracking vulnerabilities, the platform dropped support for transparent ledgers. The marketplace transitioned into an XMR-only environment, utilizing ring signatures and stealth addresses exclusively for all economic routing.
Technical Architecture
Escrow & Multisig
The platform operates a sophisticated escrow routing system. Advanced clients and merchants utilize 2-of-3 multisignature (multisig) transactions. This cryptographic arrangement prevents funds from moving without consensus from at least two participating parties, mathematically securing capital during transit and preventing centralized exit risks.
Walletless Operation
Unlike legacy platforms that required participants to deposit funds into centralized platform wallets, modern architecture implements walletless modes. Transactions are funded on a per-order basis directly from external nodes. This significantly reduces the total value locked (TVL) on internal servers, degrading the incentive for hostile intrusions.
Topological Interface Documentation
Archival captures demonstrating the utilitarian, low-bandwidth UI design implemented to maximize Tor network transmission efficiency.



Network Telemetry & Trust Metrics
Merchant Vetting
Stringent onboarding protocols require cryptographic verification and substantial operational bonds to deter malicious actors from establishing supply nodes.